On September 24th, a vulnerability was reported in the GNU Bourne-Again-Shell (BASh, or Bash), specifically a flaw with how Bash processes values of environment variables, that allows remote code execution of varying types in many common configurations. The overall risk is severe due to bash being configured for use, by default, on most Linux servers.
While Liquid Web immediately began working to proactively patch this vulnerability, some servers may remain vulnerable depending on their update settings or other unforeseen intervening factors. Thus, we’ve provided the instruction below.
To Summarize:
- This flaw exploits Bash, a Unix command-line shell run by default on most Linux servers.
- Allows for remote code execution, and many types of command-line based attacks.
- A patch is available, and your server can be easily updated.
- We have tutorials on How to Update Bash on Red Hat and CentOS and How to Update Bash on Debian and Ubuntu.
- Test the vulnerability of your server with the information below.
The National Cyber Awareness System describes the issue as follows:
GNU Bash through 4.3 bash43-025 processes trailing strings after certain malformed function definitions in the values of environment variables, which allows remote attackers to write to files or possibly have unknown other impact via a crafted environment, as demonstrated by vectors involving the ForceCommand feature in OpenSSH sshd, the mod_cgi and mod_cgid modules in the Apache HTTP Server, scripts executed by unspecified DHCP clients, and other situations in which setting the environment occurs across a privilege boundary from Bash execution. NOTE: this vulnerability exists because of an incomplete fix for CVE-2014-6271.
Again, have tutorials on How to Update Bash on Red Hat and CentOS and How to Update Bash on Debian and Ubuntu.
Additional information on CVE-2014-6271 Bash Vulnerability can be found here.
Additional information on CVE-2014-7169 Bash Vulnerability can be found here.
Ubuntu specific information can be found here.
Red Hat specific information can be found here.
CentOS specific information can be found here.
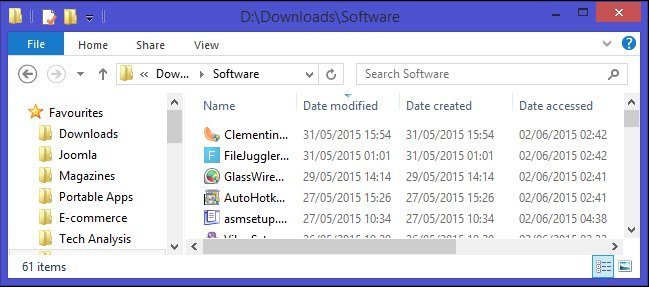
Check whether or not your server is vulnerable by running the following (safe to run) code:
env x='() { :;}; echo vulnerable' bash -c 'echo hello'
If your server isn’t vulnerable, then the following will be displayed:
bash: warning: x: ignoring function definition attempt
bash: error importing function definition for `x’
hello
If your server is vulnerable, then the following will be displayed:
vulnerable
hello
Proceed to our tutorials on How to Update Bash on Red Hat and CentOS and How to Update Bash on Debian and Ubuntu.
Want to Try This Tutorial?
Launch a Free* Storm Server
*For new customers only
Thank you. Your request has been submitted and we’ll be sending you a $75 Storm coupon shortly!





















No Comments